**TL;DR:** Securing WordPress involves multiple layers of defense: update core, themes, and plugins on WordPress 6.7, use strong passwords with two-factor authentication, install a reputable security plugin, enforce SSL, and select a host with server-level protection. Begin with Step 1 (updates) and proceed through all 10 steps to protect against common attacks.
**Last Updated: April 2026**
WordPress, powering over 43% of websites, is the most popular CMS and thus the most targeted. The WordPress.org security team notes that most compromised sites had outdated software, weak credentials, or no server protection at breach time. Fortunately, WordPress security is straightforward: follow a checklist. Complete these 10 steps to make your site significantly more secure than the average installation.
If you’re new to WordPress, start with our beginner’s guide to logging in, then return here to secure your site.
**Why WordPress Security Matters More Than Ever in 2026**
Automated bots scan millions of URLs daily for outdated plugins, default admin usernames, and exposed login pages. Site size or profitability doesn’t matter; bots target every IP address they find, exploiting vulnerabilities automatically, often injecting spam, malware, or backdoors unnoticed by site owners.
Compromised sites face consequences from embarrassment to devastation: Google blacklisting, lost customer data, hosting suspension, and hours of cleanup. The 10 steps below address common attack vectors against WordPress sites running PHP 8.3 and WordPress 6.7 in 2026.
**Step 1: Keep WordPress Core, Themes, and Plugins Updated**
Outdated software causes most successful WordPress attacks. Every update mentioning a “security fix” indicates a vulnerability in the previous version. Attackers read changelogs and scan for sites with older versions.
Enable automatic minor core updates in wp-config.php:
“`php
define( ‘WP_AUTO_UPDATE_CORE’, ‘minor’ );
“`
For plugins and themes, go to Dashboard > Updates and apply immediately. Review installed plugins quarterly and remove those not updated in over 12 months.
**Step 2: Use Strong, Unique Passwords for Every Account**
Brute force attacks guess common passwords. If your admin password is short, reused, or dictionary-based, it can be cracked. Use WordPress’s strong password generator for user accounts. A strong password in 2026 is at least 16 characters with mixed cases, numbers, and symbols.
Apply the same standard to hosting accounts, database users, FTP credentials, and emails tied to your domain. Use a password manager like Bitwarden or 1Password for secure storage.
**Step 3: Enable Two-Factor Authentication (2FA)**
Two-factor authentication adds a layer beyond passwords. Even if attackers get your password, they can’t log in without a one-time code from your authentication app. This step defeats most credential-stuffing and brute force attacks.
Plugins like WP 2FA and Two Factor make adding 2FA easy. Configure 2FA for all admin and editor accounts.
**Step 4: Install a Reputable WordPress Security Plugin**
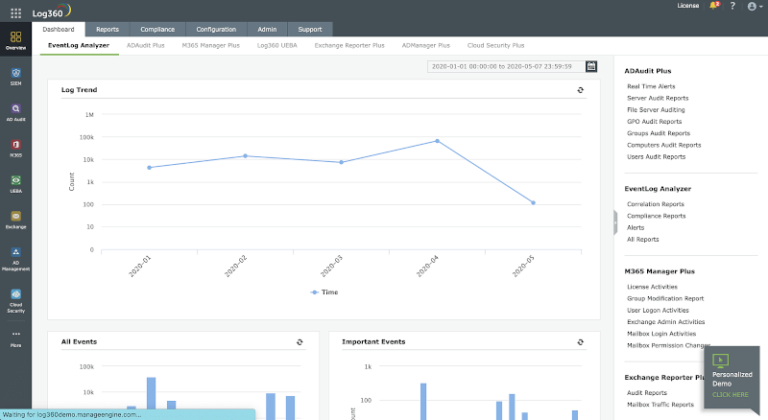
A good security plugin offers malware scanning, login attempt limiting, firewall rules, and activity logging. These act as an application-level firewall, blocking known malicious IPs and requests before they reach your site’s code.
Popular 2026 options include Wordfence Security, Sucuri Security, and Solid Security. For detailed comparisons, see our guide to the best WordPress security plugins.
**Step 5: Force HTTPS with an SSL Certificate**
Every WordPress site in 2026 should use HTTPS. An SSL certificate encrypts data between the visitor’s browser and your server, preventing man-in-the-middle attacks. Google uses HTTPS as a ranking signal and warns about HTTP sites in Chrome.
Most hosts offer free SSL certificates via Let’s Encrypt. After installing, enforce HTTPS site-wide by updating WordPress address and site address in Settings > General to use https://. Add this to .htaccess to redirect all HTTP traffic:
“`apache
RewriteEngine On
RewriteCond %{HTTPS} off
RewriteRule ^(.*)$ https://%{HTTP_HOST}%{REQUEST_URI} [L,R=301]
“`
**Step 6: Harden Your WordPress Login Page**
The default login URL (wp-login.php) is known to attackers. Bots constantly attempt credential-stuffing. Use these hardening measures:
– Limit login attempts: Block IPs after failed tries. Most security plugins offer this.
– Change the login URL: Plugins like WPS Hide Login let you customize the login path.
– Add a CAPTCHA: Google reCAPTCHA v3 or Cloudflare Turnstile stop bots without hassle for users.
– Rename the default admin username: Create a new account with a unique username, assign Administrator role, then delete “admin.”
**Step 7: Set Correct WordPress File Permissions**
Incorrect